The Future of Security_ Exploring the Biometric Verification Scale
In today's rapidly evolving technological landscape, ensuring security has become more critical than ever. With the rise of cyber threats and the increasing need for stringent identity verification, traditional security measures are proving insufficient. Enter the Biometric Verification Scale—a cutting-edge innovation that's set to redefine the landscape of security across multiple sectors.
What is Biometric Verification?
Biometric verification is a method of identifying or authenticating an individual based on unique biological traits. Unlike passwords or PINs, which can be forgotten, stolen, or guessed, biometric traits such as fingerprints, iris patterns, facial features, and even voice prints are inherently unique to each individual. These traits make biometric verification a robust, reliable, and increasingly popular choice for secure identification.
The Evolution of Biometric Verification
Biometric verification has come a long way since its initial conception. Early forms of biometric identification included rudimentary fingerprint scans, which have now evolved into sophisticated systems capable of capturing detailed, multi-dimensional data. Modern biometric verification scales integrate advanced sensors and algorithms to ensure accurate and fast identification.
The Technology Behind Biometric Verification Scales
At the heart of the biometric verification scale is a highly advanced sensor system capable of capturing detailed biological data. These sensors use infrared light, high-resolution cameras, and sometimes even 3D imaging to create a comprehensive profile of the biometric trait in question. The data captured is then processed using sophisticated algorithms that compare it to stored profiles, ensuring a match for successful verification.
Applications Across Various Sectors
Healthcare
In healthcare, biometric verification scales are revolutionizing patient identification. Traditional methods like ID cards and verbal confirmations can be prone to errors, leading to incorrect treatment or even medical identity theft. Biometric verification scales offer a more accurate and secure alternative, ensuring that patients receive the correct treatment and that medical records are protected.
Finance
The financial sector is another area where biometric verification scales are making a significant impact. Banks and financial institutions are increasingly adopting biometric verification to secure transactions and protect against fraud. From ATM withdrawals to online banking, biometric verification provides an additional layer of security, ensuring that only authorized individuals can access sensitive financial information.
Government and Public Safety
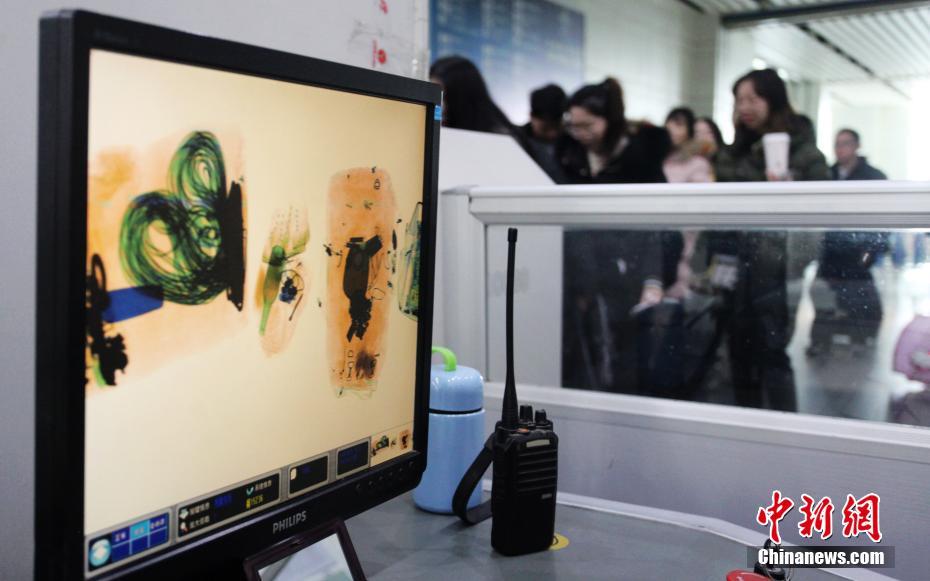
Governments and public safety agencies are leveraging biometric verification scales to secure facilities, control access to sensitive areas, and prevent unauthorized entry. In airports, for example, biometric scales can streamline security checks, reducing wait times and enhancing overall security.
Benefits of Biometric Verification
Enhanced Security
Biometric verification offers unparalleled security due to the uniqueness of biological traits. Unlike passwords, which can be easily compromised, biometric traits are difficult to replicate or steal, making them a more secure form of identification.
Convenience
For users, biometric verification provides a level of convenience that is hard to beat. Gone are the days of remembering complex passwords or carrying multiple forms of identification. A simple scan of a fingerprint or a facial recognition can grant access, making the process seamless and user-friendly.
Efficiency
Biometric verification scales also improve operational efficiency. In sectors like healthcare and finance, where time is of the essence, biometric verification can speed up processes such as patient check-ins and transaction approvals, leading to better service delivery.
The Future of Biometric Verification
As technology continues to advance, the future of biometric verification looks incredibly promising. Emerging trends such as liveness detection—which can distinguish between a real person and a fake one—are further enhancing the security and reliability of biometric systems. Additionally, the integration of biometric verification with other technologies like AI and machine learning is expected to bring even more sophisticated and efficient solutions to the table.
Addressing Concerns and Challenges
Despite its numerous benefits, biometric verification does come with some challenges and concerns. Issues such as privacy, data security, and the potential for misuse must be carefully addressed. However, with robust regulatory frameworks and advanced encryption technologies, these concerns can be mitigated, ensuring that biometric verification remains a secure and trustworthy method of identification.
Conclusion
The Biometric Verification Scale represents a significant leap forward in the field of security technology. By leveraging the unique and unchangeable nature of biological traits, these systems provide enhanced security, convenience, and efficiency across various sectors. As we move further into the digital age, biometric verification is poised to play a crucial role in safeguarding our digital and physical worlds.
In this second part of our exploration into biometric verification scales, we'll delve deeper into the technical intricacies, ethical considerations, and future trends of this groundbreaking technology. We'll uncover how biometric verification is not just shaping but redefining the future of security and privacy.
Technical Intricacies of Biometric Verification Scales
Sensor Technology
At the core of every biometric verification scale is advanced sensor technology. These sensors capture detailed biological data with high precision. For instance, fingerprint sensors use optical, capacitive, or ultrasonic methods to capture intricate details of an individual's fingerprint. Similarly, iris scanners employ infrared light to capture the unique patterns within an individual's iris. High-resolution cameras and sophisticated algorithms work in tandem to ensure accurate and reliable verification.
Algorithmic Processing
Once the biometric data is captured, it undergoes processing through advanced algorithms. These algorithms compare the live biometric data against stored profiles in a database. Machine learning and deep learning techniques play a crucial role here, enabling the algorithms to improve their accuracy over time by learning from new data.
Data Encryption
Security is paramount when dealing with biometric data. To protect this sensitive information, biometric verification scales employ advanced encryption techniques. Data is encrypted both during transmission and storage, ensuring that even if the data is intercepted or accessed without permission, it remains unreadable and secure.
Ethical Considerations
Privacy Concerns
One of the primary ethical considerations surrounding biometric verification is privacy. Biometric data is highly personal and sensitive. If this data is compromised, it can lead to significant privacy violations. Therefore, it is crucial to implement stringent data protection measures to safeguard this information.
Consent and Transparency
Obtaining informed consent from individuals whose biometric data is being collected is essential. Users should be fully aware of how their data will be used, stored, and protected. Transparency in these processes builds trust and ensures that individuals are comfortable with the level of personal information being shared.
Data Minimization
The principle of data minimization should guide the collection and use of biometric data. Only the necessary data should be collected to achieve the intended purpose, reducing the risk of data misuse and enhancing privacy.
Multi-Factor Authentication
Biometric verification scales often work in conjunction with other forms of authentication to create a multi-factor authentication system. This layered approach provides an additional layer of security, ensuring that even if one factor is compromised, the other factors remain intact. For example, a biometric verification scale can be used alongside a password or a one-time PIN to provide a more secure authentication process.
Future Trends and Innovations
Integration with AI
The integration of biometric verification scales with artificial intelligence is a promising trend. AI can enhance the accuracy of biometric data processing, detect anomalies, and even predict potential security threats. This combination can lead to more sophisticated and reliable security systems.
Cross-Platform Compatibility
Future biometric verification scales are expected to offer cross-platform compatibility, meaning they can be used across different devices and systems seamlessly. This flexibility will make biometric verification more accessible and convenient for users across various sectors.
Advancements in Liveness Detection
Liveness detection technology is another exciting development in biometric verification. This technology can distinguish between a real person and a fake one, such as a mask or a photo. By detecting signs of life and movement, liveness detection enhances the security of biometric verification systems, making them more robust against spoofing attacks.
Privacy-Preserving Biometrics
As privacy concerns grow, so does the development of privacy-preserving biometrics. Techniques such as homomorphic encryption and secure multi-party computation are being explored to allow biometric data to be used for verification without revealing the actual biometric information. This approach can enhance privacy while still providing the benefits of biometric verification.
Real-World Applications and Case Studies
Case Study: Healthcare
In the healthcare sector, biometric verification scales are proving to be invaluable. For instance, in a large hospital network, biometric verification scales are used to securely access patient records and ensure that only authorized personnel can perform critical procedures. This not only enhances patient safety but also protects sensitive medical information from unauthorized access.
Case Study: Banking
In the banking sector, biometric verification scales are being used to secure ATMs and online banking platforms. Customers can now withdraw cash or approve transactions through a simple fingerprint or facial scan, significantly reducing the risk of fraud. This convenience and security combination has led to a significant increase in customer trust and satisfaction.
Case Study: Government
未来发展方向
1. 个性化医疗
生物识别技术在个性化医疗中的应用潜力巨大。通过对个人的基因组、蛋白质组和其他生物标志物的详细分析,医生可以为患者量身定制治疗方案。例如,在癌症治疗中,生物识别技术可以帮助识别最适合某个患者的药物,从而提高治疗效果,减少副作用。
2. 智能城市
在智能城市中,生物识别技术可以用于多个领域。例如,公共交通系统可以通过面部识别技术让乘客无需购票直接乘车。在安全监控中,生物识别可以帮助识别可疑人员,提高城市的安全性。
3. 零售和电子商务
在零售和电子商务中,生物识别技术可以用于个性化推荐系统。通过分析顾客的生物特征,如购买行为、浏览历史和面部表情,系统可以提供更加贴近个人需求的产品推荐,从而提升购物体验和满意度。
4. 教育
在教育领域,生物识别技术可以用于学生的学习行为分析。例如,通过分析学生的脑电波、眼动和面部表情,教育系统可以实时了解学生的学习状态,从而调整教学方法,提供更有针对性的帮助。
技术挑战与解决方案
1. 数据隐私与安全
生物识别技术涉及大量个人敏感数据,如何保护这些数据的隐私和安全是一个重大挑战。解决方案包括采用先进的加密技术、分布式数据存储和严格的访问控制措施。
2. 准确性与可靠性
生物识别技术的准确性和可靠性直接关系到其应用的广泛性。为了提高准确性,研究人员正在开发更先进的传感器和算法,同时通过大数据和机器学习技术不断优化识别模型。
3. 伦理与法律问题
生物识别技术的广泛应用也带来了一系列伦理和法律问题,如数据使用的合法性、个人信息的自主权和算法的公平性。这需要社会各界共同制定相关法律法规,并进行广泛的伦理讨论,以确保技术的健康发展。
结论
生物识别技术正在迅速发展,并在多个领域展现出巨大的潜力。虽然面临一些技术和伦理挑战,但通过不断的技术创新和社会规范的建立,生物识别技术必将为人类社会带来更多的便利和福祉。我们期待在未来看到更多创新应用,进一步提升我们的生活质量。
In the ever-evolving world of blockchain technology, the BTC L2 Programmable Gold Rush stands out as a beacon of innovation and opportunity. This burgeoning sector of decentralized finance (DeFi) is reshaping how we think about digital currencies, pushing the boundaries of what’s possible with Layer 2 (L2) solutions.
The Dawn of a New Era
The Bitcoin network, while revolutionary, faces challenges in scalability and speed. Traditional Bitcoin transactions can be slow and expensive, limiting its usability for everyday transactions. Enter Layer 2 solutions, which aim to solve these issues by creating secondary networks that operate on top of the primary Bitcoin blockchain. These L2 solutions offer faster transaction speeds and lower fees, unlocking Bitcoin’s full potential as a versatile digital asset.
Programmable Solutions Leading the Charge
The BTC L2 Programmable Gold Rush is driven by the rise of programmable Layer 2 solutions that leverage the flexibility of smart contracts. Unlike traditional Layer 2 solutions, programmable L2s allow developers to create custom protocols and applications that can be seamlessly integrated with the Bitcoin network. This flexibility opens up a world of possibilities, from decentralized exchanges (DEXs) and lending platforms to complex financial instruments and gaming ecosystems.
Scalability Without Compromise
One of the most compelling aspects of the BTC L2 Programmable Gold Rush is scalability. By shifting some transaction processing off the main Bitcoin blockchain, these L2 solutions can handle a significantly higher volume of transactions without sacrificing speed or security. This is achieved through innovative techniques like state channels, sidechains, and rollups, each offering unique benefits and trade-offs.
State Channels: These allow multiple transactions to occur off-chain between two parties, with the final state being settled on the main blockchain. This drastically reduces the load on the Bitcoin network and lowers transaction costs. Sidechains: These are separate blockchains that run in parallel to the main Bitcoin blockchain, offering their own rules and capabilities. They can be used to experiment with new technologies or applications without risking the stability of the main network. Rollups: These bundle many transactions into a single block on the main chain, drastically reducing the amount of data that needs to be stored and processed. This not only enhances scalability but also preserves the security of the main Bitcoin blockchain.
Empowering Developers and Innovators
The BTC L2 Programmable Gold Rush is not just about technology; it’s about empowerment. Developers and innovators are at the heart of this movement, using the flexibility of programmable L2 solutions to build new and exciting applications. This democratization of blockchain technology means that anyone with an idea can bring it to life, potentially disrupting traditional industries and creating new economic models.
Smart Contracts: The Backbone of the Gold Rush
Smart contracts play a crucial role in the BTC L2 Programmable Gold Rush. These self-executing contracts with the terms of the agreement directly written into code enable a wide range of applications without the need for intermediaries. From automated savings plans to complex trading algorithms, smart contracts are the backbone of the new DeFi ecosystem built on L2 solutions.
The Future Unfolds
The BTC L2 Programmable Gold Rush represents a transformative shift in the blockchain landscape. As more developers and businesses explore the potential of Layer 2 solutions, we can expect to see a surge in innovative applications that leverage the scalability, speed, and flexibility of programmable L2s.
The future of decentralized finance is bright, with the BTC L2 Programmable Gold Rush at its forefront. By addressing the limitations of the Bitcoin network and unlocking its true potential, this new wave of blockchain innovation promises to redefine the digital economy.
Stay tuned for the second part of our exploration into the BTC L2 Programmable Gold Rush, where we’ll dive deeper into specific examples and case studies of groundbreaking projects making waves in this exciting frontier.
The Golden Age of Innovation
In the second installment of our exploration into the BTC L2 Programmable Gold Rush, we’ll delve deeper into the groundbreaking projects and innovations that are shaping this new era of decentralized finance. These projects are not only pushing the boundaries of what’s possible but also paving the way for a more inclusive and efficient digital economy.
Real-World Applications and Case Studies
Let’s take a closer look at some of the most exciting projects and applications that are driving the BTC L2 Programmable Gold Rush.
1. Decentralized Exchanges (DEXs)
Decentralized exchanges are a cornerstone of the DeFi ecosystem, and Layer 2 solutions are playing a pivotal role in enhancing their functionality and efficiency. By leveraging L2 technology, DEXs can offer faster transaction speeds and lower fees, making them more attractive to users.
Uniswap on Layer 2: Uniswap, one of the most popular DEXs, has begun exploring Layer 2 solutions to improve its scalability. By moving some of its operations off-chain, Uniswap can handle more trades per second and reduce transaction costs, providing a smoother experience for users.
2. Lending and Borrowing Platforms
Lending and borrowing platforms are another key area where BTC L2 solutions are making a significant impact. These platforms allow users to earn interest on their idle Bitcoin or borrow BTC against collateral, all without relying on traditional financial institutions.
Aave on Layer 2: Aave, a leading decentralized lending platform, is exploring Layer 2 solutions to enhance its scalability and reduce transaction fees. By integrating with L2 networks, Aave aims to offer a more seamless and cost-effective lending experience.
3. Gaming and NFTs
The intersection of blockchain technology and gaming has given rise to a new wave of innovative applications, and Layer 2 solutions are playing a crucial role in this space. From play-to-earn games to decentralized marketplaces for non-fungible tokens (NFTs), the potential is immense.
Decentraland on Layer 2: Decentraland, a virtual reality platform built on the Ethereum blockchain, is exploring Layer 2 solutions to improve its scalability and reduce transaction costs. By leveraging L2 technology, Decentraland can offer a more responsive and affordable experience for users.
4. Cross-Chain Solutions
One of the biggest challenges in the blockchain world is interoperability between different blockchain networks. Layer 2 solutions are at the forefront of developing cross-chain solutions that enable seamless communication and transactions between different blockchains.
Polkadot and BTC L2: Polkadot, a multi-chain platform that enables different blockchains to interoperate, is collaborating with BTC L2 solutions to create bridges that allow Bitcoin to interact with other blockchains. This opens up new possibilities for cross-chain transactions and decentralized applications.
The Role of Community and Collaboration
The success of the BTC L2 Programmable Gold Rush hinges on community and collaboration. Open-source projects and decentralized autonomous organizations (DAOs) are playing a crucial role in driving innovation and fostering a sense of shared purpose.
Open-Source Development: Many BTC L2 projects are open-source, allowing developers from around the world to contribute to their development and improvement. This collaborative approach accelerates innovation and ensures that the best ideas and technologies are brought to the forefront. DAOs: Decentralized autonomous organizations are playing an increasingly important role in funding and supporting BTC L2 projects. By pooling resources and making collective decisions, DAOs can drive significant progress and ensure that the most impactful projects receive the support they need.
Challenges and Opportunities Ahead
While the BTC L2 Programmable Gold Rush is full of promise, it’s not without its challenges. Scalability, security, and regulatory concerns are all significant hurdles that need to be addressed to ensure the long-term success of these innovative solutions.
Scalability
As more users and applications join the BTC L2 network, scalability will remain a critical challenge. Developers are continuously working on improving L2 solutions to handle increased transaction volumes without compromising speed or security.
Security
Security is paramount in the blockchain world, and Layer 2 solutions are no exception. Ensuring the security of off-chain transactions and protecting users’ assets are top priorities for developers and researchers.
Regulatory Challenges
The regulatory landscape for blockchain technology is still evolving, and navigating these complex regulations is a significant challenge for BTC L2 projects. Ensuring compliance while maintaining innovation is a delicate balance that requires ongoing collaboration with regulators and industry stakeholders.
The Road Ahead
The BTC L2 Programmable Gold Rush is a testament to the power of innovation and collaboration in the blockchain space. As we’ve seen, the potential of Layer 2 solutions is vast, from enhancing the functionality of DeFi platforms to enabling new and exciting applications in gaming, finance, and beyond.
The future of decentralized finance is bright, with BTC L2 solutions at the heart of this new wave of blockchain innovation. By addressing the challenges of scalability, security, and regulation, we can unlock the full potential of these solutions and create a more inclusive and efficient digital economy.
As we look ahead, the BTC L2 Programmable Gold Rush will continue to drive innovation and shape the future of decentralized finance. Whether you’re a developer, investor, or enthusiast, there’s never been a better time to be part of this exciting frontier.
Thank you for joining us on this journey through the BTC L2 Programmable Gold Rush. Stay tuned for more insights and updates as we continue to explorethe Future of BTC L2 Programmable Solutions
As we look to the future, the BTC L2 Programmable Gold Rush is set to transform the landscape of decentralized finance and beyond. The ongoing advancements in Layer 2 solutions, coupled with the creative and collaborative spirit of the blockchain community, promise to drive unprecedented innovation and growth. Here, we explore some of the most exciting prospects and potential developments on the horizon.
Enhanced User Experience
One of the primary goals of BTC L2 solutions is to provide a seamless and user-friendly experience. By moving transaction processing off the main blockchain, these solutions can offer faster transaction speeds and lower fees, making them more accessible to everyday users. This enhanced user experience is crucial for mainstream adoption.
Interoperability and Cross-Chain Solutions
Interoperability is a key challenge in the blockchain world, and BTC L2 solutions are at the forefront of developing cross-chain solutions. As we’ve seen with projects like Polkadot, these solutions aim to create bridges that allow different blockchains to communicate and transact with one another. This interoperability will enable a more connected and integrated blockchain ecosystem, opening up new possibilities for decentralized applications and services.
Advanced Smart Contracts and Decentralized Applications
The flexibility of programmable Layer 2 solutions means that developers can create complex and advanced smart contracts and decentralized applications (dApps). From decentralized finance (DeFi) platforms to gaming ecosystems and beyond, the potential is immense. These advanced dApps can offer new economic models, streamline processes, and create entirely new industries.
Ecosystem Growth and Ecosystem Development
As BTC L2 solutions mature, we can expect to see significant growth in the ecosystem. More developers will be attracted to the platform, leading to a surge in new projects and innovations. This growth will be fueled by the robust infrastructure and the supportive community that surrounds BTC L2 solutions.
Regulatory Adaptation and Compliance
Navigating the regulatory landscape will be crucial for the future success of BTC L2 solutions. As governments and regulatory bodies begin to understand and adopt blockchain technology, there will be a need for clear and consistent regulations that foster innovation while protecting users. Collaborative efforts between industry stakeholders and regulators will be essential to create a balanced regulatory environment.
Environmental Sustainability
Scalability and efficiency are not just technical challenges; they also have environmental implications. By reducing the load on the main Bitcoin blockchain, BTC L2 solutions can contribute to a more sustainable and eco-friendly blockchain ecosystem. Innovations in energy-efficient consensus mechanisms and the use of renewable energy sources will further enhance the environmental footprint of these solutions.
Global Impact and Economic Inclusion
The BTC L2 Programmable Gold Rush has the potential to drive significant global impact, particularly in regions with limited access to traditional financial services. By providing a decentralized and accessible financial infrastructure, BTC L2 solutions can empower individuals in underserved communities, fostering economic inclusion and growth.
Conclusion
The BTC L2 Programmable Gold Rush is more than just a technological advancement; it’s a movement that’s reshaping the future of digital currencies and decentralized finance. With its focus on scalability, interoperability, and innovation, BTC L2 solutions are set to unlock new possibilities and drive the next wave of blockchain evolution.
As we continue to explore this exciting frontier, it’s clear that the BTC L2 Programmable Gold Rush is not just a trend; it’s a revolution. Whether you’re a developer, investor, or enthusiast, there’s never been a better time to be part of this transformative journey.
Stay tuned for more insights and updates as we continue to witness the unfolding story of the BTC L2 Programmable Gold Rush. The future is bright, and the potential is limitless.
DeFi Financial Inclusion AI Payments Win_ Revolutionizing Access and Transactions
AA Experience Breakthrough – Gold Rush_ Unleashing the Goldmine Within